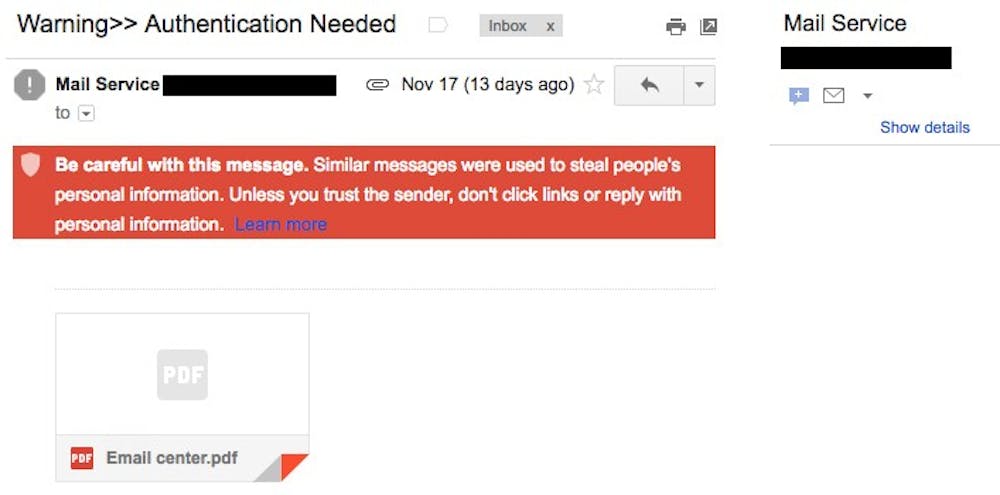
Email scams have become increasingly prevalent in recent years among members of the University community. Many students and faculty members have received “phishing” messages, which appear to come from trusted sources but are actually scams.
These emails usually ask for sensitive information such as usernames, passwords or other protected materials.
University Chief Information Security Officer Jason Belford said phishing messages have not only infiltrated the University email accounts, but other organizations as well.
“The ‘bad guys’ have realized that they can circumvent the technical controls by obtaining user credentials,” Belford said in an email statement. “Most recently, I have seen fake iTunes, Facebook, UPS and FedEx emails trick unsuspecting users.”
Belford sent an email Monday warning students of phishing emails. Within the next few days, students will be sent an email message that resembles a real phishing message. If one “fails” by inputting sensitive information, they will undergo on-screen training about how to identify and prevent phishing scams.
“If successful, these phishing campaigns put users and the University's data and reputation at risk,” Belford said in his email to the University community.
The University’s Information Security, Policy and Records Office and Information Technology Services have instituted multiple preventive measures against phishing and spam. For example, the University student information search has recently become more private. Users must go through NetBadge in order to see student information.
“While this decision was not specifically related to phishing, I believe it will have an effect where our students will receive fewer phishing emails,” Belford said.
The ISPRO and ITS anti-phishing user education program has also been initiated, which Belford said includes the phishing simulation exercises.
“Many of our peers in academia have been running phishing simulations for years. We recently ran a simulation for U.Va.’s faculty and staff,” Belford said. “The next phase of this project is to send this message to our students. The purpose of this simulation is strictly a training exercise.”
Fourth-year College student Anna Dorsey said her University email was hacked twice last year. After the first hack, all of her contacts received an email from Dorsey asking them to click on a Google Doc she made.
“I do not recall ever opening an email that alerted me I was hacked or even seemed like a ‘phishing’ email,” Dorsey said. “I only remember being aware I was hacked when everyone contacted me asking if I meant to send them the Google Doc attachment.”
Dorsey said she immediately changed all of her passwords after the initial hack in order to prevent future incidents. Her email account, however, was hacked again over spring break. After this second hack, a full body email was sent to multiple contacts that resembled a traditional phishing email.
“This hacker caused my entire email account to be shut down and I no longer could log into Collab or SIS,” Dorsey said. “I not only had to go through the University to regain access to my email, but also the University then directed me to Apple. So now I have a very long and random password with every character they allow you to use just so I don't get hacked for the third time.”
Dorsey said she was unsure if a training program would have helped because not all phishing emails are the same or even recognizable.
“On the other hand, I think the threat of having to enroll in a University study due to opening a phishing email is an incentive in itself for students to become more aware about not opening suspicious emails,” she said.
Belford said the training program would educate students about how to determine whether an email message is fraudulent or not.
“My hopes are that the data from this exercise will help us determine where we should focus future training,” Belford said. “For example, if we find that more people respond to our phishing message from mobile phones then we can concentrate on the phishing training and mobile phones.”