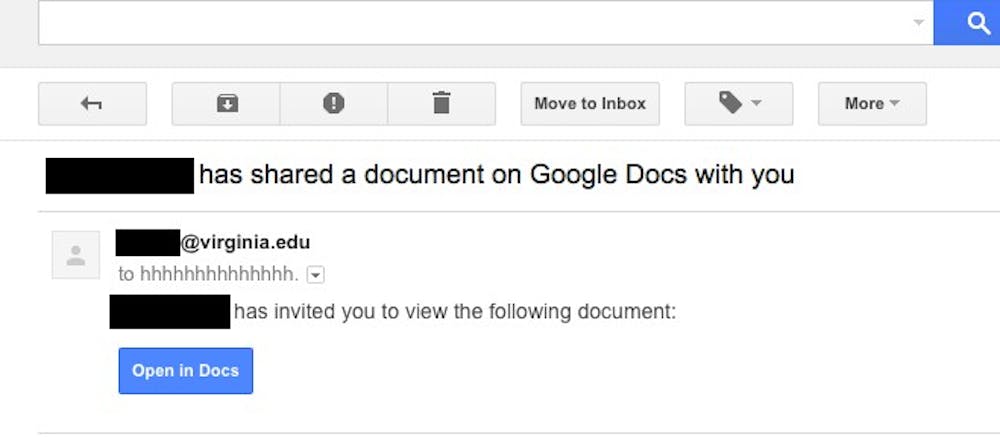
Several students at the University were impacted by a national phishing email scam Wednesday. While the emails were sent from a suspicious, non-University address, they appeared to be messages from Google Docs that used the names of people familiar with the recipient to make the message seem credible.
Students across Grounds found the emails to be convincing, including first-year College student Emily May, who received a phishing message which appeared to be distributed by a CIO.
“I received the email from one of my club presidents,” May said. “I saw the strange address and that I was ‘bbc:’ but I assumed it was a forwarding mechanism. I was wrong.”
Second-year College student Dana Clements also thought the emails looked credible, but did not open them because she had been warned by a friend.
“The email seemed believable because it looked like any regular Google doc,” Clements said. “And even though I was not expecting a Google doc, it seemed possible that some person from one of my classes could have sent that out to all of us, and since it had mod-U.Va. in the title I probably wouldn’t have thought twice about opening it.”
If a student clicked the link, he or she would have been redirected to a verification page asking for permission before hijacking the account.
“It took me to a verification page that looked quite like Google Docs,” May said. “I was a little suspicious since it took a long time to load.”
Jason Belford, chief information security officer for Information Technology Services, noted that the cyber attack was not limited to the University, and ITS did what it could do to prevent the attack.
“It wasn’t isolated to us,” Belford said. “Our system did exactly what it was supposed to do. It let the first few through, and then it started what we call greylisting, and it wasn’t letting a lot of them through. There is a lot more that could’ve gotten through had the system caved in like they were supposed to.”
Belford said it’s difficult to know the number of students affected, largely because it is possible that students did not open it while on the University’s network.
“I know of a couple dozen, at least,” Belford said. “Some of it is were, ‘they on our network when they did it?’ If they did it on our network we would have more insight, because we can see into it. Some of it was self-reported.”
Belford noted that because this recent scam has worked, it will not be the last of its kind.
“Once these things work one time, you’re going to have copycats and these things are going to progress,” Belford said.
ITS began a phishing education program last fall to inform the University community about scam emails and what to look for. Belford recommends that students question the validity and purpose of applications asking for permissions in the future.
“If an application wants permission to something, even if it’s just your microphone, question,” Belford said. “Think, ‘Why does this thing want to use my microphone?’ You really just need to stop and read things and think about what you’re giving permission to.”
Clements said the scam hasn’t impacted how she feels about the security of her University email account.
“I think U.Va. has done a lot to warn us about phishing, but I probably would have still clicked the link had I not been warned by a friend,” Clements said. “I still believe my email is secure, it’s just a matter of being vigilant against scam mail.”